If you are looking for an effective way to
get rid of Trojan.FakeMS.ED, read this post, you will get both manual and
automatic removal guide to erase this nasty computer infection completely from
your system.
Brief Intruduction
Trojan.FakeMS.ED is a risky Trojan virus
that has been widely spread in the Internet. Your computer may be infected with
this harmful infection when downloading free software, clicking unknown links,
checking spam email.
Once your computer gets entangled by Trojan.FakeMS.ED, it may bring a lot of troubles to the infected computer and harass computer users at all points.
- It is a nasty Trojan installs without your consent;
- It may show fake security messages to bring in rogue antivirus.
- It displays annoying pop-ups while you surf the web.
- It violates your privacy and compromises your security.
- It may allow access for the remote host by installing hidden FTP server.
In brief, Trojan.FakeMS.ED is a hazardous Trojan horse that cause large amounts of damages. When encountering this pest, you should remove it as fast as you can to protect system data integrity. The longer Trojan.FakeMS.ED stays in the system, the more damages it will make. Do not wait until Windows is completely ruined.
Removal Guide
The following passage is going to offer TWO useful instructions on removing Trojan.FakeMS.ED for you. Free to choose the one you prefer to help you to fix the issue.
- Option One: Trojan.FakeMS.ED Manual Removal Instruction
- Option Two: Trojan.FakeMS.ED Automatic Removal Instruction Using SpyHunter
Option One: Trojan.FakeMS.ED Manual Removal Instruction
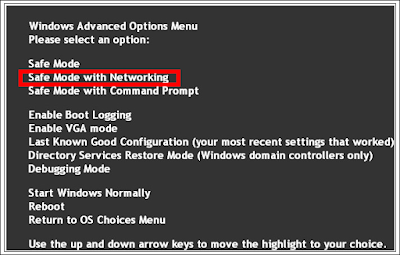
Step 1. Restart the computer and put it in Safe mode with Networking
Restart the computer and start hitting F8 key repeatedly when PC is booting up again; if successfully, Safe mode options will show up on the screen for you to select. Please use arrow keys to highlight Safe mode with Networking option and hit enter key. System will be loading files into this mode afterward.
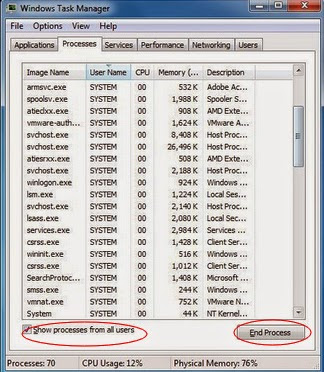
Step 2. End all the harmful running processes
Open task manager by pressing Alt+Ctrl+Del keys at the same time. Another way is to click on the Start button and choose Run option, then type taskmgr into and press OK. Stop all the suspicious running processes.
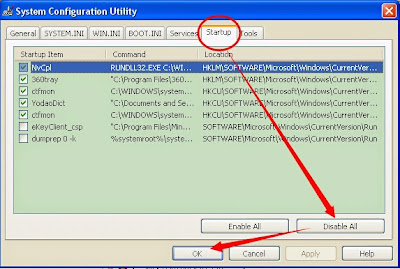
Step 3. Disable any suspicious startup items that are made by Trojan.FakeMS.ED
Click Start menu; click Run; type: msconfig in the Run box; click OK to open the System Configuration Utility; Disable all possible startup items generated.
Step 5. Show hidden files and folders and delete all the following files.
Guide: click the Start button and choose Control Panel, clicking Appearance and Personalization, to find Folder Options then double-click on it. In the pop-up dialog box, click the View tab and uncheck Hide protected operating system files (Recommended).

Step 6. Remove all the malicious registry entries as follows:
Open Registry Editor to delete all the registries as below Guide: open Registry Editor by pressing Window+R keys together.(another way is clicking on the Start button and choosing Run option, then typing into Regedit and pressing Enter.)
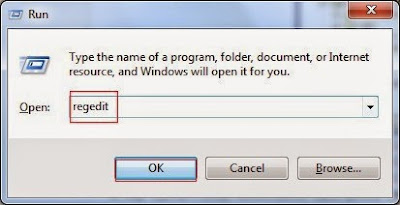
Delete all the vicious registries as below:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msmpeng.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msseces.exe
HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon "Shell" = "%AppData%\.exe"
HKLM\SOFTWARE\Classes\AppID\.exe
Step 7. Reset your web browsers to clear your internet history records, internet temp files and cookies.
Internet Explorer:
Open Internet Explorer, click the Gear icon or Tools > Internet options. Here, go to the Advanced tab and click the Reset button. Go to the Reset Internet Explorer settings > Delete personal settings and click on Reset option. Finally, click Close and OK to save the changes.
Mozilla Firefox:
Open Mozilla Firefox, go to the Help section > Troubleshooting Information. Here, select Reset Firefox and click Finish.
Google Chrome:
Open Google Chrome, click the Chrome menu button, select Tools > Extensions, find unknown extension and remove them by clicking Recycle bin. Now click Settings > Show Advanced settings > Reset browser settings and click Reset.
There may be some other issues such as windows registry errors in your system. To avoid potential risk and to ensure your computer security, you are suggested to use RegCure Pro to optimize your system after the threat removal.
Step 8. Optimize your PC using RegCure Pro
What can RegCure Pro do for you?
- Fix system errors
- Remove malware
- Improve startup
- Defrag memory
- Clean up your PC
1. Click the below button to download RegCure Pro to your PC.
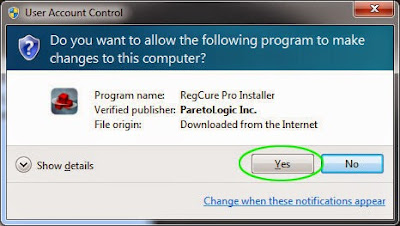
2. Click the Yes button to enter in installation process and then follow the instruction to install the program step by step.
3. When the program is successfully installed, double click on its desktop shortcut to open it. On the Overview tab, check all the scan settings and then click on the Click to Start Scan button to run a system scan on your computer.
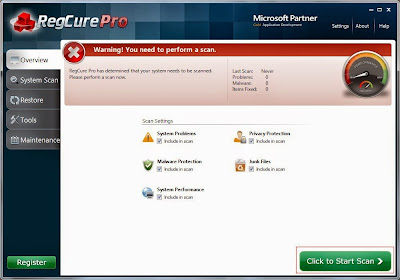
4. The first system scan will take some time, please be patient. The screenshot of the system scan progress is shown below.

5. When the system scan is done, click on Fix All button to completely remove all the performance problems in your computer.

>> Click Here to Download RegCure Pro to Fix Slow PC Performance! <<
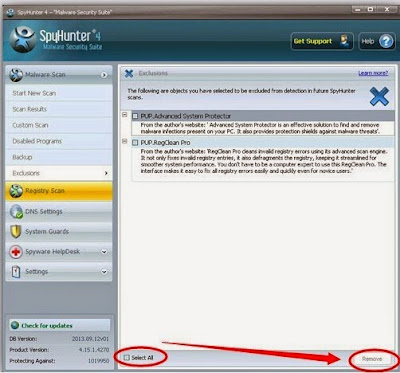
Option Two: Trojan.FakeMS.ED Automatic Removal Instruction Using SpyHunter
What can SpyHunter do for you?
- Give your PC intuitive real-time protection.
- Detect, remove and block spyware, rootkits, adware, keyloggers, cookies, trojans, worms and other types of malware.
- Spyware HelpDesk generates free custom malware fixes specific to your PC
- Allow you to restore backed up objects.
Step 1. Click on the below button to free download SpyHunter on your PC.
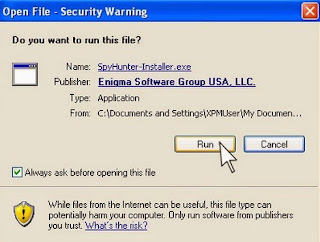
Step 2. Click the Run button to enter the setup program and follow the installation steps until setup is complete.
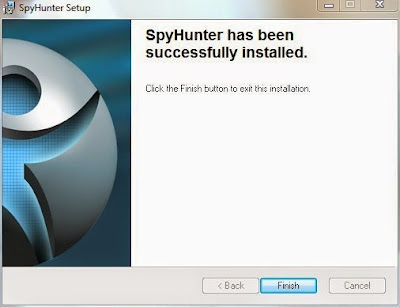
Step 3. When the installation is complete, click the Finish button to exit the installation.


Step 5. Allow the program to scan by clicking the Scan Computer Now! button. If you would like to have a quick scan on your PC, please check the Quick Scan box; otherwise, uncheck it.

Step 6. The first scan will take some time, please be patient while waiting for the scanning result.

>>Click Here to Download SpyHunter to Try All the Features!<<


No comments:
Post a Comment