What is Win32/zperm?
Win32/zperm is an extremely harmful Trojan virus which is designed by cyber criminals to pursue their evil purposes by stealing valuable information stored in the targeted PC and even conducting a series of malicious tasks to damage the PC seriously.
- It imposes certain changes in the system.
- It drops harmful files under System folder of Windows.
- It may show fake security messages to entice you.
- It may display numerous annoying advertisements.
- It makes your PC more vulnerable and be easy to be controlled by remote users.
- It violates your privacy and compromises your security
- It uses a backdoor to bring more malicious infections to seriously damage your computer.
How to fully remove Win32/zperm from Windows?
- Option One: Win32/zperm Manual Removal Instruction
- Option Two: Win32/zperm Automatic Removal Instruction Using SpyHunter
Option One: Win32/zperm Manual Removal Instruction
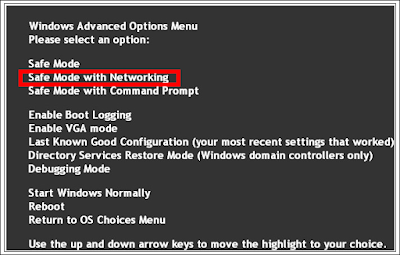
Step 1. Restart the computer and put it in Safe mode with Networking
Restart the computer and start hitting F8 key repeatedly when PC is booting up again; if successfully, Safe mode options will show up on the screen for you to select. Please use arrow keys to highlight Safe mode with Networking option and hit enter key. System will be loading files into this mode afterward.
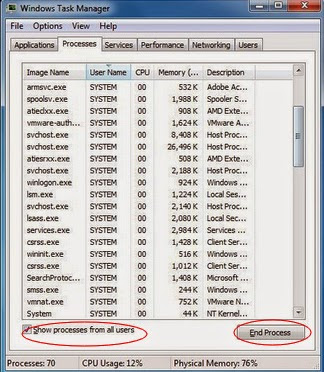
Step 2. End all the harmful running processes
Open task manager by pressing Alt+Ctrl+Del keys at the same time. Another way is to click on the Start button and choose Run option, then type taskmgr into and press OK. Stop all the suspicious running processes.
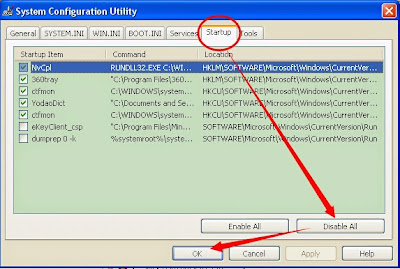
Step 3. Disable any suspicious startup items that are made by Win32/zperm
Click Start menu; click Run; type: msconfig in the Run box; click OK to open the System Configuration Utility; Disable all possible startup items generated.
Step 5. Show hidden files and folders and delete all the following files.
Guide: click the Start button and choose Control Panel, clicking Appearance and Personalization, to find Folder Options then double-click on it. In the pop-up dialog box, click the View tab and uncheck Hide protected operating system files (Recommended).

Step 6. Remove all the malicious registry entries as follows:
Open Registry Editor to delete all the registries as below Guide: open Registry Editor by pressing Window+R keys together.(another way is clicking on the Start button and choosing Run option, then typing into Regedit and pressing Enter.)
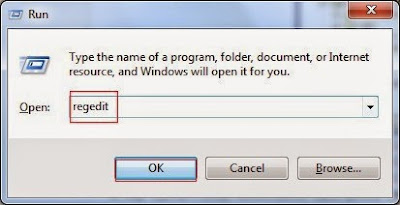
Delete all the vicious registries as below:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msmpeng.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msseces.exe
HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon "Shell" = "%AppData%\.exe"
HKLM\SOFTWARE\Classes\AppID\.exe
There may be some other issues such as windows registry errors in your system. To avoid potential risk and to ensure your computer security, you are suggested to use RegCure Pro to optimize your system after the threat removal.
Step 7. Optimize your PC using RegCure Pro
What can RegCure Pro do for you?
- Fix system errors
- Remove malware
- Improve startup
- Defrag memory
- Clean up your PC
1. Click the below button to download RegCure Pro to your PC.
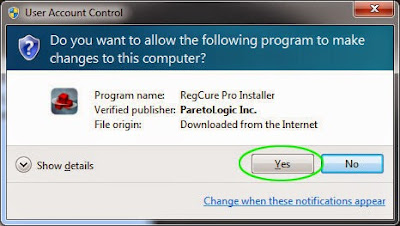
2. Click the Yes button to enter in installation process and then follow the instruction to install the program step by step.
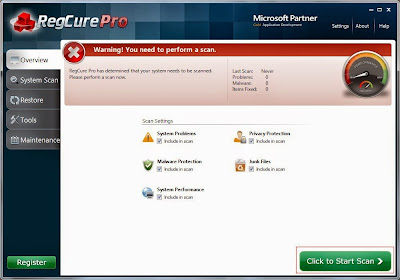
3. When the program is successfully installed, double click on its desktop shortcut to open it. On the Overview tab, check all the scan settings and then click on the Click to Start Scan button to run a system scan on your computer.
4. The first system scan will take some time, please be patient. The screenshot of the system scan progress is shown below.

5. When the system scan is done, click on Fix All button to completely remove all the performance problems in your computer.

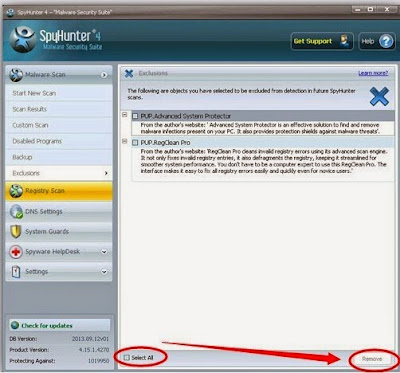
Option Two: Win32/zperm Automatic Removal Instruction Using SpyHunter
What can SpyHunter do for you?
- Give your PC intuitive real-time protection.
- Detect, remove and block spyware, rootkits, adware, keyloggers, cookies, trojans, worms and other types of malware.
- Spyware HelpDesk generates free custom malware fixes specific to your PC
- Allow you to restore backed up objects.
Step 1. Click on the below button to free download SpyHunter on your PC.
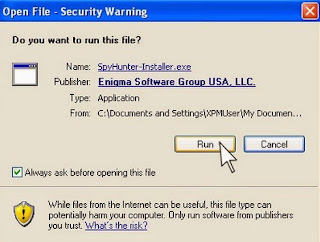
Step 2. Click the Run button to enter the setup program and follow the installation steps until setup is complete.
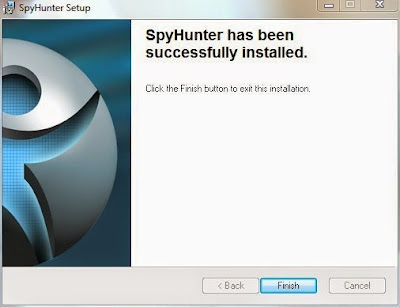
Step 3. When the installation is complete, click the Finish button to exit the installation.


Step 5. Allow the program to scan by clicking the Scan Computer Now! button. If you would like to have a quick scan on your PC, please check the Quick Scan box; otherwise, uncheck it.

Step 6. The first scan will take some time, please be patient while waiting for the scanning result.

In Conclusion:
The longer you keep Win32/zperm in your computer, the more chaos would be brought to crash the system. When encountering this Trojan virus or any other malicious virus, the best action you should take is to remove the virus immediately.
Download SpyHunter to Kill Win32/zperm!


No comments:
Post a Comment